Applications Built tough for countless applications.
Each of our memory products is built to survive extreme conditions
and deliver over a wide range of applications.

Access Control (with audit trail)
When used as a credential, Datakey Secure Memory devices provide more robust security than a simple PIN or password, and unlike mag-stripe or prox-card solutions, Datakey devices use read/write memory, so audit trail data can be logged back to the credential (as well as the host). This is ideal in non-networked applications, as a user’s audit trail information is available each time the credential is used.

Data Logging
The unique form factor and robust nature of Datakey portable memory products make them a perfect solution for embedded data logging applications, especially those in harsh environments. Log operational, performance and use data. Unlike SD cards and USB flash drives, the unique form factor of the RUGGEDrive™ memory devices discourage theft and provide a base level of security, as they won't plug directly in to standard computer ports.

User Rights/Preferences/Settings
When used in identification applications, Datakey Secure Memory products not only identify the user, they can also store the user’s preferred settings for that machine, allowing every machine that a user works on to be configured automatically to his/her personalized settings. Datakey memory devices can also store rights information, only allowing the user access to the functions they have been trained on.

Secure Data Transfer
For secure data transfer applications, the UFX RUGGEDrive™ memory token functions just like a USB flash drive, but has additional security features not found on consumer flash drives. The product's unique form-factor means that it won’t plug directly into a standard USB port, and its unique serial number can be used for user ID and for encrypting the onboard data.

Medical Disposable Authentication
Protect patient safety and OEM revenue from counterfeit devices by including Serial Memory or Secure Memory tokens with your medical consumables. The host validates the consumable by reading the product authentication information stored on the token. The robust token can be sterilized right along with the consumable!
Authentication Dongle
Remember when PC software applications required a parallel port dongle in order to work? If your embedded application could benefit from a similar security solution, we have Secure Memory devices with varying levels of security features and memory capacities to choose from. Let us help you implement a subscription revenue model using one of our removable memory devices.
Usage Tracking/Limiting
Datakey memory devices can be tethered to disposable medical products that have a finite lifespan. Unlike bar codes and most RFID tags, Datakey products use re-writable memory, so usage data can be written back to the device over time, ensuring the disposable is not used more than the specified amount. Specialized Serial Memory tokens withstand all major sterilization methods.

Cashless Vending/Transactions
Purchasing without cash is a common occurrence thanks to the popularity of credit cards. When a cashless purchase option is desired, but the user base doesn’t use credit cards or the required phone/network connection is not possible (or practical), our Secure Memory line has got you covered.

Model Identification
Industrial and medical devices often have host controller units that support multiple attachments. Each attachment may have unique operational characteristics, calibration parameters or required device settings. Tethered Serial Memory tokens automatically identify the model and type of attachment and relay the proper information about the attachment to the host.

Parameter/Settings Upload
Avoid dangerous and costly configuration mistakes from manually entering device settings. Datakey Serial Memory solutions excel at providing a reliable and consistent way to upload device parameters and calibration data. Prevent mistakes by having the proper information automatically uploaded when the memory device is inserted.

Parameter/Settings Backup (Cloning)
Minimize downtime by storing all of a deployed controller’s settings/programmed parameters on a rugged Serial Memory device in the field. Should the controller ever need replacing, the settings from the first controller can be uploaded into the new controller on the spot, quickly turning the new controller into a clone of the old one.

Calibration Data Upload
When each of your products are truly unique, our rugged Serial Memory tokens can electronically store each product’s specific calibration data. Even if your product lives in harsh environments, our rugged memory devices are up to the task.

Positively Linking Wireless Devices
When it’s critical to establish a positive link between two wireless devices, such as medical devices where the proper pairing of a transmitter and receiver is critical, Datakey' Serial Memory tokens are the ideal solution. They make it easy to send ID information between the receiving and transmitting wireless devices. High cycle-life receptacles allow multiple pairings per day.

Program Upload
Datakey RUGGEDrive™ memory tokens provide a rugged and secure way of transporting program information from the office to the field, whether it’s GPS route information for a tractor or mission data for a military computer.

Feature Enable
Datakey Secure Memory devices make it easy for your customers to buy your base model and later pay for upgrades, all with the same hardware. You can ship your product with all application features, but only enable those features your customers pay for. Then you can turn on additional features after the product has been deployed by simply shipping out a feature-activation token.
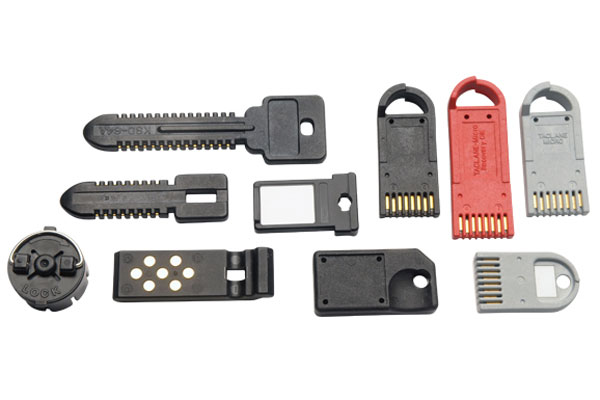
Crypto Ignition Key
Datakey Serial Memory products have been the de facto standard for cryptographic ignition key (CIK) implementations since the late 1980s because of their proven ruggedness, reliability and long-term availability. A CIK is a device or electronic key that is used to unlock the secure mode of cryptographic equipment such as network encryptors, key loaders, secure telephones and more.
Firmware Updates
Datakey's Serial Memory products make it easy to update the firmware of your products, even if they aren’t connected to the Internet. All you have to do is add a low-cost Datakey receptacle to the control board and send out a memory token containing the firmware update.