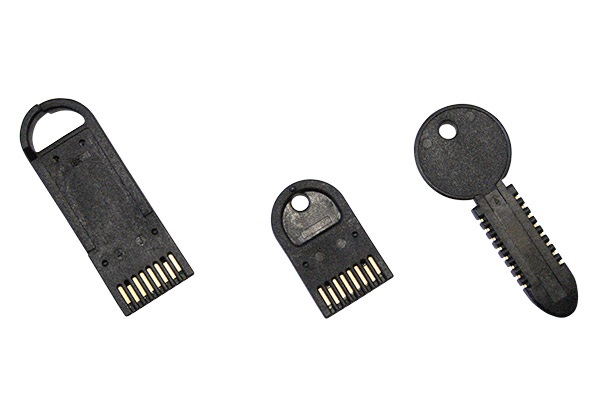
Secure Memory Authentication and Data
Security for OEMs
The Secure Memory line provides a range of security features, from EEPROM devices with pre-programmed, non-changeable serial numbers to those with on-board encryption, password-protected memory, mutual authentication and tamper protection circuits.
More Than Just a Serial Number /
All Secure Memory keys and tokens contain a unique serial number, but that’s not what makes these products unique. It is the additional, re-writable, non-volatile memory and advanced security and authentication features that make these products a much more powerful credential than read-only devices like mag-stripe cards or RFID badges. Here is just a sampling of ways to use our Secure Memory devices:
Two Factor Authentication
A CryptoAuthentication™ memory token is an ideal solution for embedded systems requiring multi-factor authentication (aka two factor authentication) for user access. One factor may be a PIN or a password and the other a physical credential—the memory token. The token can securely store the PIN/password, eliminating the need for the embedded system to store these locally or retrieve them off a remote server. Other information like rights to certain functions/features can also be securely stored on the token. Even temporary keys that are good for only a certain number of uses are possible with this powerful authentication solution.
Secure Feature-Enable
It can be beneficial to have one configuration of hardware and firmware that can be used across a variety of products/models. Various features can be enabled or disabled during provisioning at the factory. In addition to certain manufacturing efficiencies, this design can enable customers to turn on more advanced functions and capabilities down the road post-purchase. In this scenario, a customer purchases the new or expanded functionality. The manufacturer sends out a secure Datakey CryptoAuthentication™ memory token that, when plugged into the controller and authenticated, turns on the purchased functionality.
View additional applications for more ideas and possibilities with Secure Memory.